# Setting up MIRACL Trust SSO as an Identity Provider Within Open Telekom Cloud
These instructions are up-to-date at the time of writing, but you should refer back to official OTC documentation to check for any changes. We cannot guarantee the accuracy of our SP-specific guidance.
-
Log in to the Open Telekom Cloud management console.
-
Choose Mgmt & Deployment > Identity and Access Management.
-
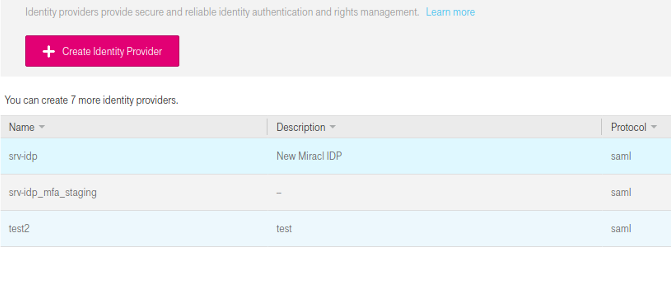
In the navigation pane, choose Identity Provider The following window is displayed.
-
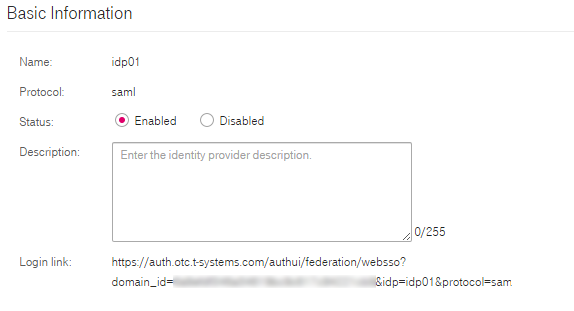
Click Create Identity Provider The following dialog box is displayed.
-
Set Name, Protocol(SAML), and Status(enabled) and fill in Description(optional).
-
Click OK. A confirmation message is displayed which disappears after a few seconds.
-
Click the Edit link against the IdP that was just created.
-
Upload the MIRACL Trust metadata by pointing to the locally saved .xml file:
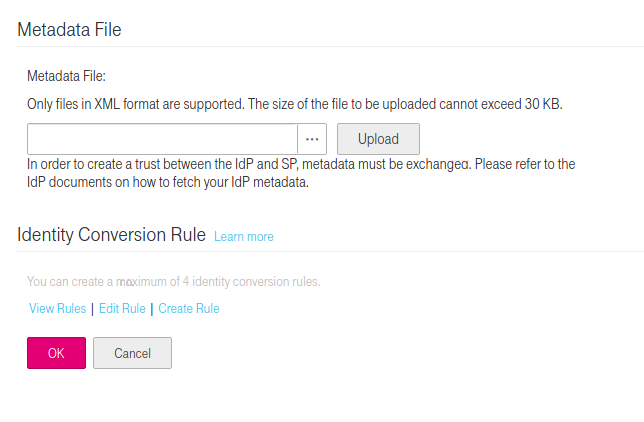
The metadata can be downloaded from
http://<yourssoip>/metadata. Note that, for a production setup, if you manually download your IdP metadata file, the validUntil date at the top of the file needs to be edited to an appropriate date (it defaults to 48hrs from the current date). -
Set the Identity Conversion Rule by clicking on Edit Rule. The following Identity Conversion Rule is based on a regular expression and would let anyone with identity
@yourcompany.comdomain log in.[ { "local": [ { "user": { "name": "{0}" } }, { "group": { "name": "{1}" } } ], "remote": [ { "type": "__NAMEID__" }, { "type": "groups" }, { "any_one_of": [ ".*@yourcompany.com" ], "regex": true, "type": "__NAMEID__" } ] } ]
# Configuring Your Open Telekom Cloud Profile With MIRACL Trust SSO
-
Edit
/etc/miracl-sso/service_providers/otc.yaml:profile: attribute: tsystems_otc_admin: >- <AttributeStatement> <Attribute FriendlyName="mail" Name="urn:oid:0.9.2342.19200300.100.1.3" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:uri"> <AttributeValue>{{.SessionUserEmail}}</AttributeValue> </Attribute> <Attribute FriendlyName="groups" Name="urn:oid:1.3.6.1.4.1.5923.1.1.1.6" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:uri"> <AttributeValue>restricted</AttributeValue> </Attribute> </AttributeStatement> sp: otc: description: T-Systems OTC name: OTC relay_state: "" login_url: https://auth.otc.t-systems.com/authui/federation/websso?domain_id=***&idp=miracl-sso&protocol=saml logout_url: https://console.otc.t-systems.com/iam/logout metadata: >- <!-- insert downloaded SP metatadata here --> sign_response: true sign_assertion: false encrypt_assertion: true authorize: - - email: ^[^@]+@example.com$ profile: attribute: tsystems_otc_admin -
Note that the name under which the SP is registered in the sp section is used to create your IdP-initiated login url, i.e.
https://<yourssoip>/login/otc. -
The above login_url is what has been issued to you by the OTC admin console, as seen in point 4 in the first section of this guide.
-
Note also that the previously configured SAML attribute is invoked with attribute: tsystems_otc_admin.
-
The OTC SP metadata is available from https://auth.otc.t-systems.com/authui/saml/metadata.xml and should be pasted into the above metadata field.
If you are using JSON format for your config file, the downloaded XML file must be converted to a single line and the " characters need to be escaped with \ to meet the json structure requirements. This can be achieved by running the following command on the downloaded metadata.xml file:
echo -e "\n"$(cat metadata.xml | tr -d '\n' | sed -E 's/"/\\"/g')"\n"The contents then are output in the terminal in a format that can be pasted into the metadata field of a JSON file.
-
In the authorize subsection, you can control what users are allowed to attempt login by following one or both of the below steps:
- Call up an LDAP setup from an
ldap.yamlfile stored in/etc/miracl-sso/integrations. - Configure a regex list of email addresses/domains. The above config shows
an example of how you would use
email: ^[^@]+@example.com$to only allow users from a certain email domain to login.
Note that if this is not set correctly, you receive ‘unauthorized user’ messages.
For more detailed info on using LDAP, API and/or regex to control authorized users, please see the authorization menu section .
- Call up an LDAP setup from an
-
Save and close the file.
-
In your /etc/miracl-sso/config.yaml file make sure you add
otc.yamlto the list of ‘includes’:includes: - core.yaml # service providers - service_providers/otc.yaml -
As always after config changes, restart the server .
-
Now your service is configured, you can visit
https://<yourssoip>/login/otcorhttps://<yourssoip>/servicesto log in to the service using IdP-initiated login, or visit the OTC login page and SP-initiated login are triggered automatically. -
You are able to login using the in-browser PIN pad or with the MIRACL Trust app. When logging in to your SSO service for the first time you are asked to register an email address so as to confirm your identity and register you as a user.