# Setting up MIRACL Trust SSO as an Identity Provider Within Okta
These instructions are up-to-date at the time of writing, but you should refer back to the official Okta documentation to check for any changes. We cannot guarantee the accuracy of our SP-specific guidance.
-
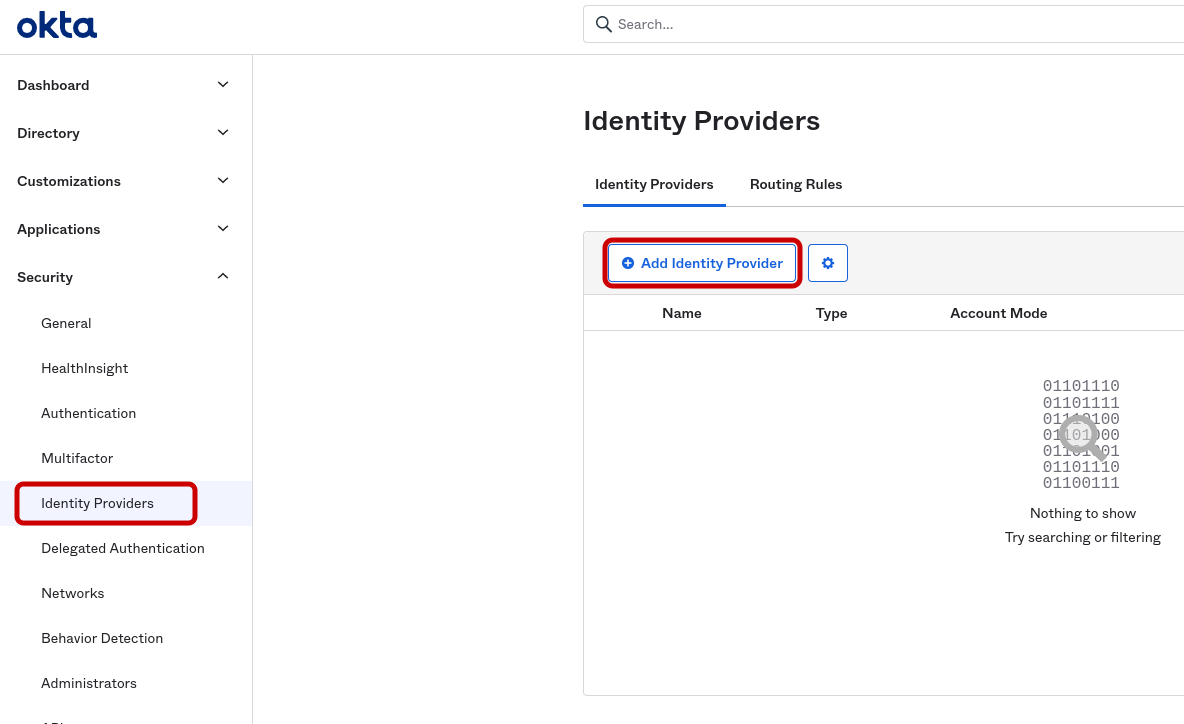
Log in to the Okta developer administration console -
https://{YourDomain}-admin.okta.com/ -
Click on Security > Identity Providers:
-
Click on ‘Add Identity Provider’, choose SAML and click Next.
-
Fill in the details as below:
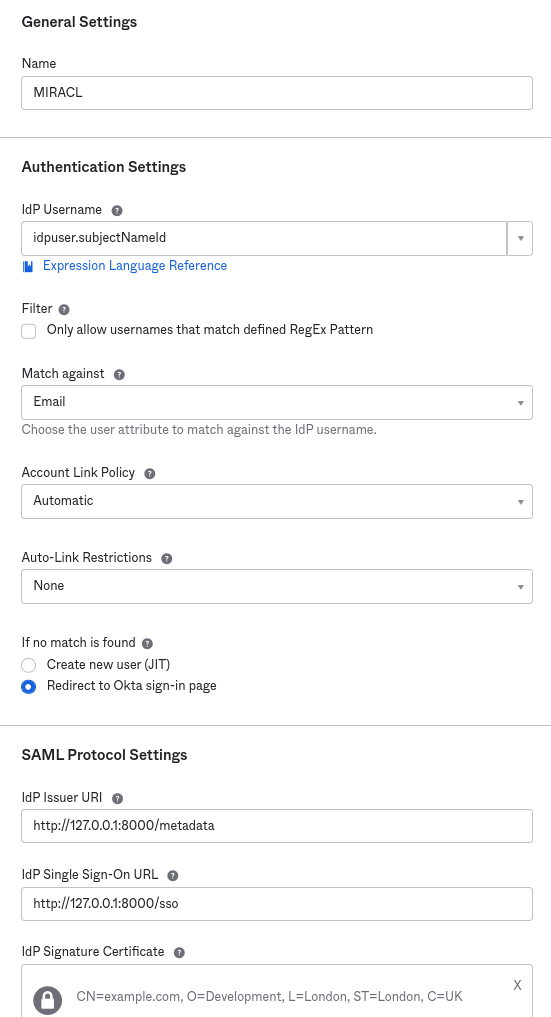
IdP Username and Match against should be set as above, as MIRACL Trust SSO only uses email to identify users.
IdP Issuer URI should be
https://<yourssoip>/metadataand IdP Single Sign-On URI should behttps://<yourssoip>/sso.IdP Signature Certificate is your idp.crt public certificate which you create as per the instructions in the Installation/Quick Start section of this documentation .
-
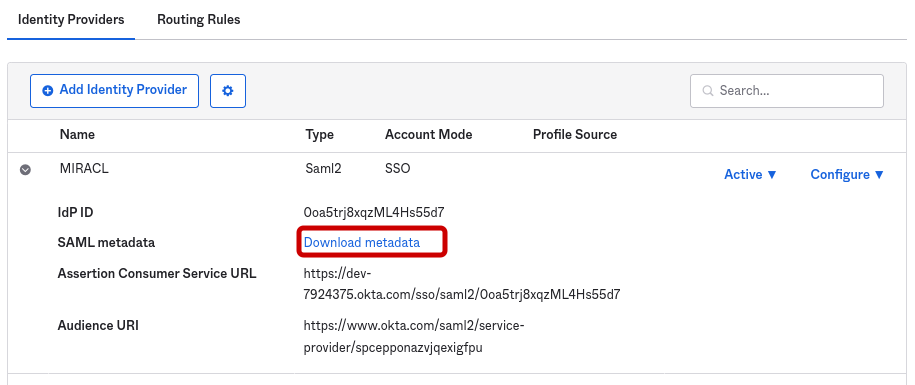
On returning to the list of IdPs, you can now download Okta’s SP metadata to be added to your IdP config:
-
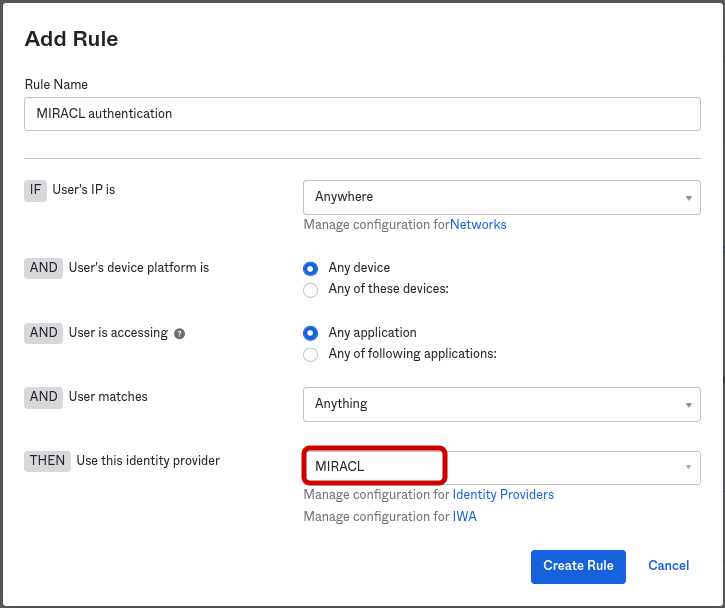
As a final step, be sure to click on the Routing Rules tab and specify when to apply your Identity Provider:
# Configuring Your Okta Service Provider Profile With MIRACL Trust SSO SAML
-
Edit
/etc/miracl-sso/service_providers/okta.yaml:sp: okta: description: Okta name: Okta relay_state: "" login_url: https://example-admin.oktapreview.com logout_url: https://example.oktapreview.com/login/signout metadata: >- <!-- insert downloaded SP metatadata here --> sign_response: true sign_assertion: false encrypt_assertion: false authorize: - - email: ^[^@]+@example.com$ -
Note that the name under which the SP is registered in the sp section is used to create your IdP-initiated login url, i.e.
https://<yourssoip>/login/okta. -
login_url is simply the url of your Okta account, while logout_url is the the url of your Okta account with
/login/signoutappended. -
The Okta SP metadata is available via the Okta download metadata link and should be pasted into the above metadata field.
Note that if you are working with json config files rather than yaml, then once you have downloaded the metadata and saved it as e.g. okta_metadata.xml, it is necessary to convert it to single line format and escape all " characters before copying and pasting it as the above metadata parameter for the Okta SP. This can be done with the following command:
echo -e "\n"$(cat okta_metadata.xml | tr -d '\n' | sed -E 's/"/\\"/g')"\n"The contents then are output in the terminal in a format that can be pasted into the metadata field of a JSON file.
-
In the authorize subsection, you can control what users are allowed to attempt login by following one or both of the below steps:
- Call up an LDAP setup from an
ldap.yamlfile stored in/etc/miracl-sso/integrations. - Configure a regex list of email addresses/domains. The above config shows
an example of how you would use
email: ^[^@]+@example.com$to only allow users from a certain email domain to login.
Note that if this is not set correctly, you receive ‘unauthorized user’ messages.
For more detailed info on using LDAP, API and/or regex to control authorized users, please see the authorization menu section .
- Call up an LDAP setup from an
-
Save and close the file.
-
In your /etc/miracl-sso/config.yaml file make sure you add
okta.yamlto the list of ‘includes’:includes: - core.yaml # service providers - service_providers/okta.yaml -
As always after config changes, restart the server .
-
Now your service is configured, you can visit
https://<yourssoip>/login/oktaorhttps://<yourssoip>/servicesto log in to the service using IdP-initiated login, or visit the Okta login page and SP-initiated login are triggered automatically. -
You are able to login using the in-browser PIN pad or with the MIRACL Trust app. When logging in to your SSO service for the first time you are asked to register an email address so as to confirm your identity and register you as a user.